Recent JavaScript Packages Compromised by Malware Attack
Recently, over 18 popular JavaScript code packages, collectively downloaded more than a billion times, were compromised due to a developer’s account being hacked. The attack was primarily aimed at stealing cryptocurrency, but experts caution that such breaches could lead to more destructive forms of malware that are tougher to identify and eliminate.
Aikido, a Belgian security firm, monitors updates in major open-source code repositories for suspicious activity. They revealed in a blog post that at least 18 widely-used code libraries on the Node Package Manager (npm) were infected with malicious code.
JavaScript, a powerful scripting language, is essential for creating interactive web experiences, like submitting forms. Developers often rely on existing code packages from npm, avoiding the need to start from scratch.
The danger arises when cybercriminals obtain npm credentials from developers. If an attacker injects malicious code into a site using one of these compromised libraries, they can gain control over a user’s browser activities.
Aikido identified that the injected code secretly intercepted cryptocurrency transactions. It manipulated wallet interactions, altering payment destinations and ensuring that funds redirected to the attacker’s accounts, all without notifying the user.
According to Aikido researcher Charlie Eriksen, this malware operates on multiple levels, messing with both application APIs and displayed content on the websites. Even if everything seems normal on the surface, transactions might be redirected behind the scenes.
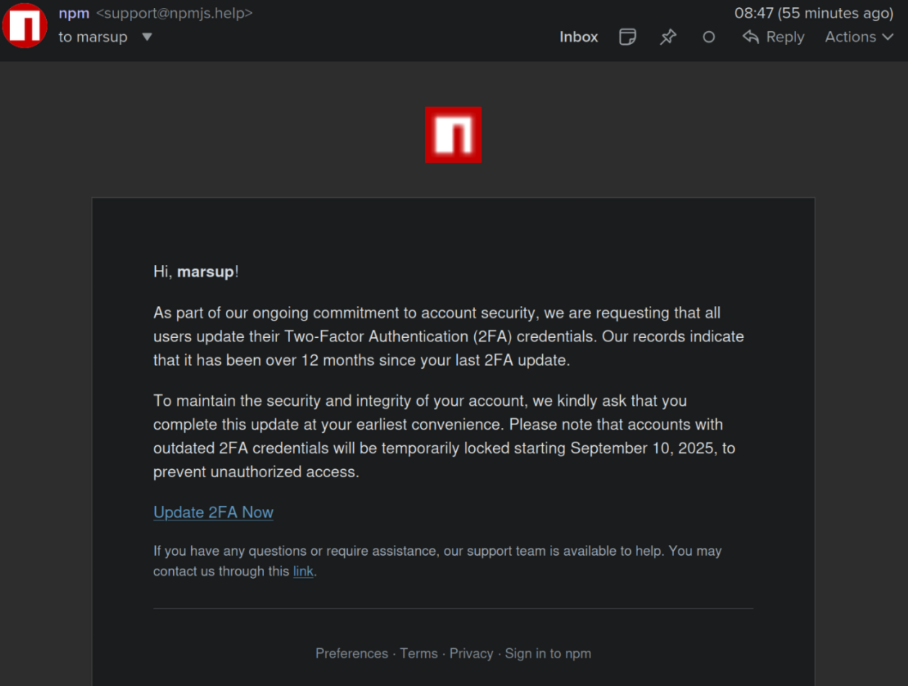
Aikido contacted affected developers through BSKY. One developer, Josh Junon, realized he had fallen victim to a phishing scheme. The phishing email deceived several individuals into upgrading their two-factor authentication by spoofing the npm login page and capturing their credentials.
Junon promptly acknowledged his mistake on a community platform, telling fellow coders, “Hello, yes, I’ve been pwned.” He expressed embarrassment, noting that the attack felt targeted.
Philippe Cathergli, a security consultant, pointed out that the attacker quickly registered a spoofed website, which was used to launch phishing emails. This kind of tactic poses a significant threat since a compromised website can be devastating for many applications and users.
Cathergli remarked on the irony that such a widespread attack aimed at a few cryptocurrencies could have had graver consequences. Eriksen agreed, highlighting that many websites narrowly avoided disaster since the situation was managed swiftly. He mentioned a previous attack on the npm developers that involved another malicious code targeting authentication tokens from various platforms.
Eriksen advocates for stricter measures, suggesting that platforms like GitHub and npm need to validate the authenticity of code submissions more rigorously. This would help ensure that new code comes directly from trusted sources, rather than relying solely on the account holder’s integrity.
He also shared concerns that after such incidents, many developers might abandon their projects, feeling overwhelmed and distrustful of the system. “People are likely to say, ‘I’m done with this package,’” he noted.
Kevin Beaumont, a noted security expert, reflected on the situation, emphasizing that many systems remain reliant on a plethora of interconnected libraries developed over many years. He highlighted the shift over the past couple of years towards AI-assisted coding, which sometimes leads to less oversight and more vulnerabilities.
Aikido has since introduced a product aimed at verifying code libraries for malware before they are deployed. Nicholas Weaver, a researcher at the International Computer Science Institute, noted that as long as developers continue to use basic forms of two-factor authentication, supply chain compromises will persist.
Weaver strongly advocates for improved security measures, calling for npm to adopt fishproof authentication methods, which would require a physical security key to log in. This would potentially safeguard against unauthorized access, even if login credentials are compromised.
“All critical infrastructures need to implement fishproof 2FA, especially given the dependencies of modern software and repositories like npm,” he stated.