There's nothing to worry about in life without the added stress and fear of finding out that your friends, family, or complete strangers are receiving text messages from “you” without your knowledge. There is enough. How did they do that? How did they send text messages from your phone without you knowing?
This is a real threat that many people face every day. That's why I felt it was so important to answer this question sent to me by John.
“I just found a text written to me. It was a reply to a text I sent. The question is, I didn't send that text? I'm 65 years old. , I'm not as active as I used to be, but I do.'' I don't remember ever sending a text message. Her wife is trying to convince me that I'm crazy. She says it's impossible for someone to send a text message (impersonating me) even though she doesn't own my phone. Is it true? Someone hacked your phone and sent you texts? ? “- John, Fort Myers, Florida
Click to get the free Cyberguy Newsletter in your cart, including security alerts, quick video tips, tech reviews, and easy how-tos to get smarter
What is SMS spoofing?
John, I am sorry to hear that you are in this situation. Even if someone doesn't own your phone, they could impersonate you and send you text messages.This is known as SMS spoofing, and This is a technique used by cybercriminals to send fraudulent text messages.
How does SMS spoofing work?
SMS spoofing involves manipulating the sender ID of a text message to make it appear as if it was sent from a different phone number. This can be done using various online services that allow users to send text messages using fake sender IDs. Cybercriminals change sender IDs to impersonate friends, family, or legitimate companies.
Example screenshot of a text message from a hacker posing as a bank (Kurt “Cyber Guy” Knutson)
It is important to note that SMS spoofing is illegal and can be used for malicious purposes, including: Phishing scam, identity theft, and fraud. Scammers use a combination of familiarity and urgency to get you to interact with the text by clicking a link, downloading a file, or replying with personal information.
How to spot and avoid SMS impersonation scams
Here are the top three reasons why scammers often use fake sender IDs to send text messages with urgent requests:
1. Make them click on a malicious link. You may be redirected to malicious websites where your personal and financial information may be stolen or even compromised. malware or virus to your phone.
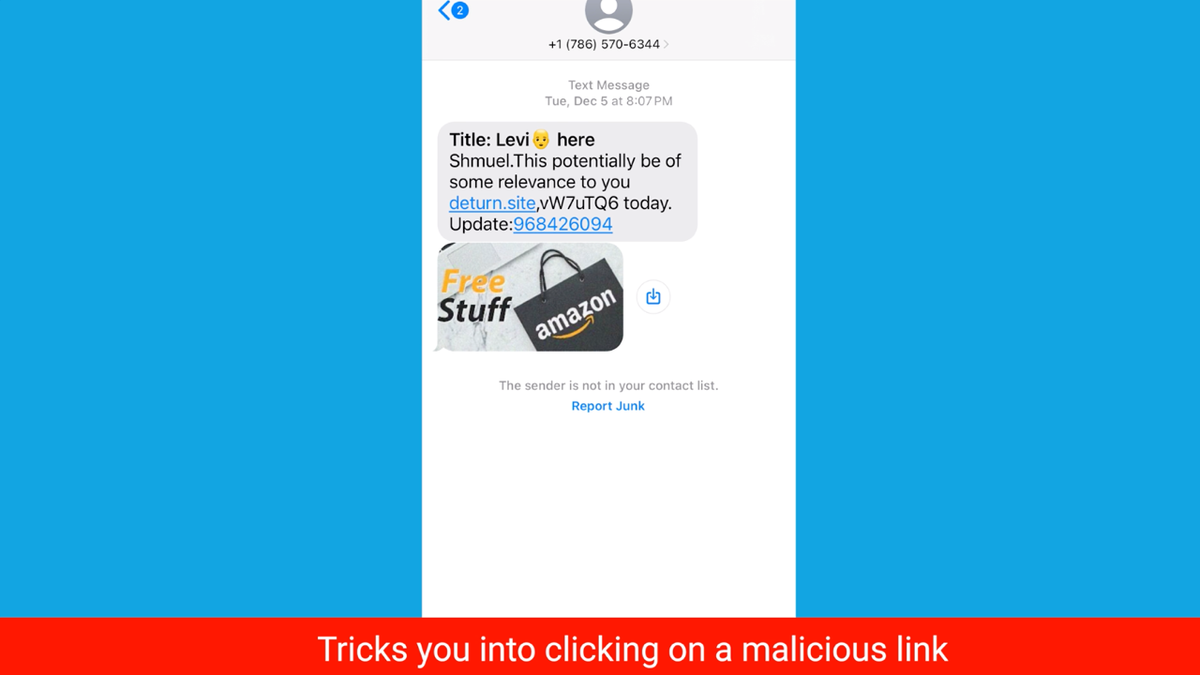
Screenshot of text SMS spoofing trying to trick you into clicking a malicious link (Kurt “Cyber Guy” Knutson)
2. Luring you into paying a fake invoice Pretending to be a reputable or familiar company.
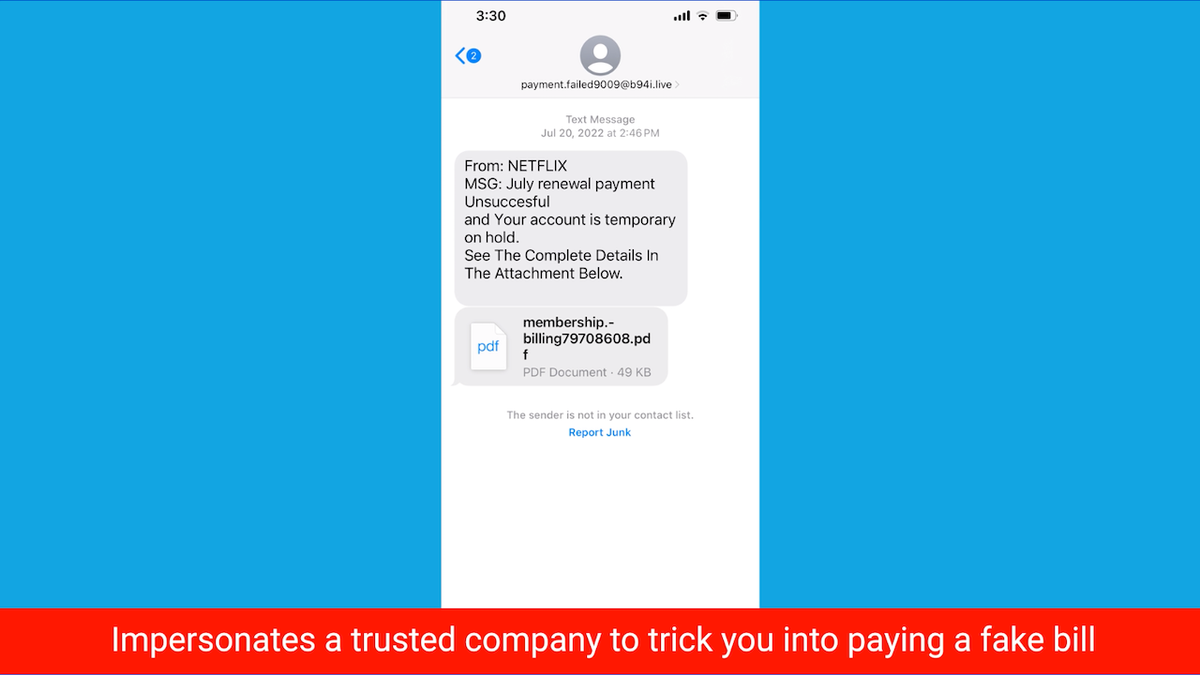
Screenshot of text spoofing to trick you into paying a fake bill (Kurt “Cyber Guy” Knutson)
3. Damage your reputation and relationships Send harmful messages to embarrass your friends, family, and others.
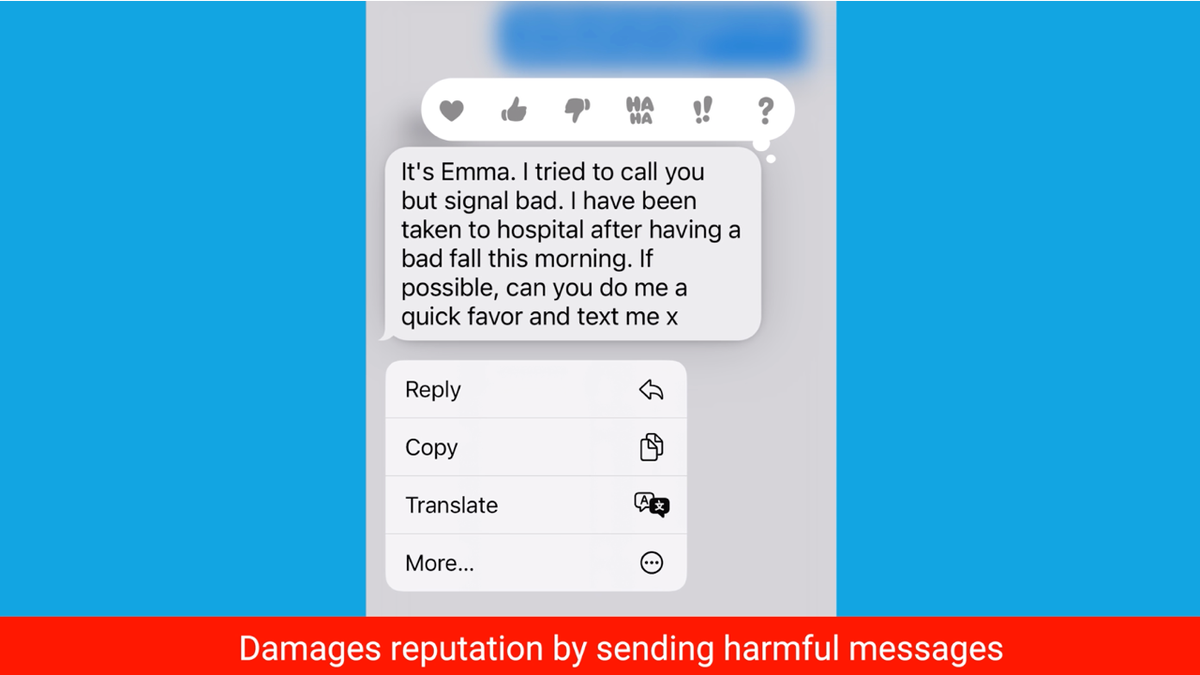
Screenshot of spoofed text attempting to damage reputation (Kurt “Cyber Guy” Knutson)
iMessage vulnerabilities
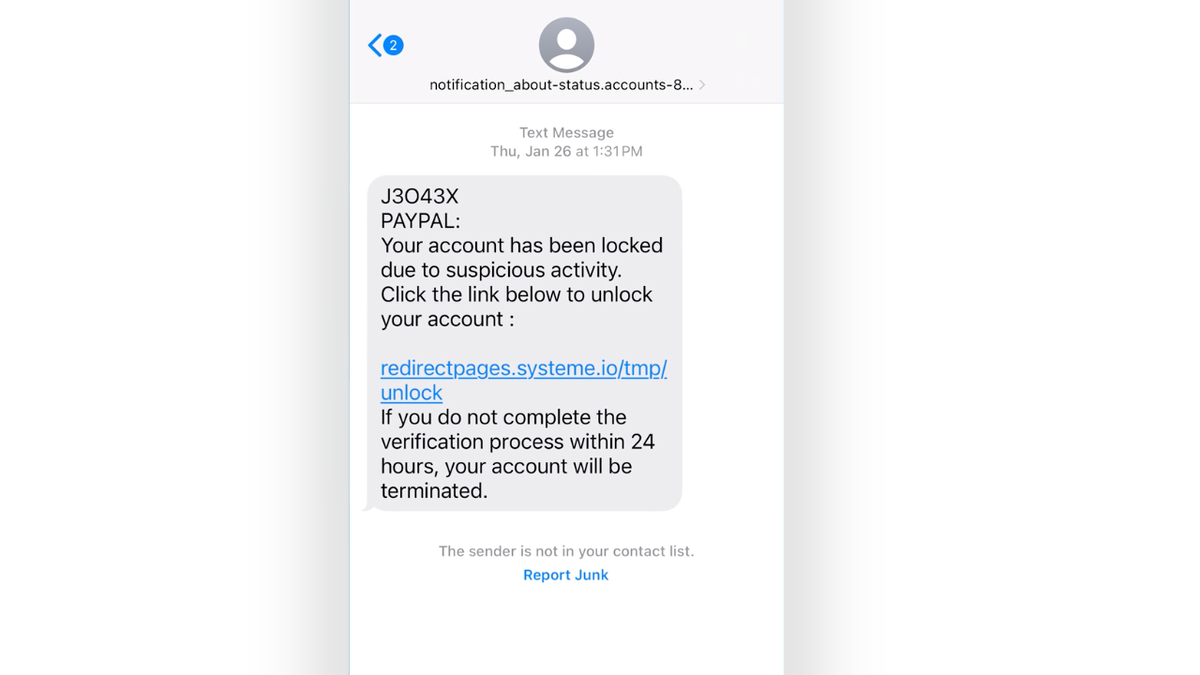
SMS spoofing of Apple devices by hackers posing as financial institutions (Kurt “Cyber Guy” Knutson)
Previously, many Apple devices were considered virtually immune to viruses and malware. Unfortunately, a bug in iOS allows a hacker to take over someone's device, just like any other device on the market. Apple patches these vulnerabilities regularly, which also makes iPhone users vulnerable to her SMS spoofing.
Hackers can exploit the “interactionless” bug to send specially crafted SMS messages, and the iMessage server can send user-specific data, such as images or SMS messages, back to the hacker. Users don't even have to open the message for this bug to take effect. Additionally, hackers can send malicious code through text and embed it on users' phones. These vulnerabilities are specific to Apple devices.
Aside from specific vulnerabilities, hackers typically require users to interact with text messages before malicious code can be unleashed on their devices.
More information: See and detect if someone you know is spying on your iPhone
7 actions to take if you suspect SMS spoofing
If you suspect that your phone has been hacked or that someone is impersonating you, it is important to take action immediately. Here are some steps you can take.
1) Install good antivirus software on your phone. Having good antivirus software actively running on your device will warn you about malware in your system and prevent you from clicking on malicious links that can install malware on your device and allow hackers to access your personal information. I warn you. Read our review of Best Antivirus Protection here.
2) Keep your phone's software updated. Both iPhone and Android users need to maintain their phone's OS and apps updated regularly Apple and Google release patches when vulnerabilities are discovered. Updating your phone can prevent hackers from exploiting security flaws and sending text messages from your phone without your knowledge.
3) Change your password. Change the passwords for all your online accounts, including email, social media, and bank accounts.Must not be used Information that is easy to guess birthday, address, etc. Use strong, unique passwords that are difficult to guess. Preferably alphanumeric, including special symbols if applicable. Make sure to run this on another device in case you have any issues. malware ahYour phone is monitoring you. Please consider using . password manager Generate and save complex passwords. It helps you create unique, hard-to-crack passwords that hackers can never guess.
4) Enable two-factor authentication. activation two-factor authentication Adding it to all your online accounts adds an extra layer of security to your accounts, making it more difficult for hackers to gain access.
5) Contact your mobile phone carrier. Contact your mobile phone carrier and report the incident. You may be able to identify the source of the text message and take appropriate action.
6) File a police report. If you believe you have been a victim of identity theft or fraud, please file a police report with your local law enforcement agency.

Fraud detection text message alerts on iPhone (Kurt “Cyber Guy” Knutson)
7) Pay attention to the connections. Do not connect if possible Unsecured or public Wi-Fi hotspots Or Bluetooth connection. Turn off the Bluetooth connection when not in use. Most iPhones let you choose who receives your files and photos. air drop (Bluetooth feature) Select to receive from no one, people in your contacts, or everyone. We recommend setting it to “No one joins” and turning it on only if you're with someone you want to send or receive files or photos from.
Read more: Protect your passwords: CHERRYBLOS; Fake trade malware threatens Android
I was fooled by a spoofed SMS. What's next?
Below are the next steps if you or someone you love determines that you are the victim of identity theft via an SMS spoofing attack.
1) Change your password. If your phone has been hacked or you suspect someone is pretending to be you, that person may be able to access your online accounts and steal your data and money. On another device (such as a laptop or desktop), you should change the passwords for all important accounts, such as email, banking, and social media. I would like to do this on a separate device so hackers don't record it. Set a new password on your hacked device. Use strong, unique passwords that are difficult to guess or crack. You may also consider using . password manager Generate passwords and store them securely.
2) Read bank statements and confirm account transactions with checks See where outlier activity started.
3) Use fraud prevention services. Identity theft companies monitor your personal information, such as your social security number (SSN), phone number, and email address, and alert you if it is sold on the dark web or used to open an account. Masu. It can also help freeze bank and credit card accounts to prevent further misuse by criminals.
The best parts of using an identity theft protection service include identity theft insurance to cover your losses and legal costs, and a white glove fraud resolution team with a US-based case manager to help you recover your losses . Check out our tips and recommendations on how to protect yourself from identity theft.
Four) Report violation to public government agencies such as the Federal Communications Commission;
Five) You should seek professional advice from a lawyer. Please be careful before contacting law enforcement, especially if you are dealing with identity theft and are unable to secure employment or housing because you are the victim of identity theft.
6) Alert all three major credit bureaus And it could also put a fraud alert on your credit report.
7) Run your own background check Or, if you discover that your information was used by a criminal, request a copy.
8) Alert your contacts. If a hacker gains access to your device through SMS spoofing, they can use it to send spam or phishing messages to your contacts. They may pretend to be you and ask for money or personal information. You should alert your contacts and warn them not to open or reply to messages from you that seem suspicious or unusual.
9) Restore your device as Factory settings. If you want to make sure your device is completely free of malware and spyware, you can restore your device to factory settings. This will erase all data and settings and reinstall the original version.you should return Up Restore important data before doing this and only restore from trusted sources.
If you are a victim of identity theft, the most important thing to do is to take immediate action to mitigate the damage and prevent further damage.
More information: How to tell if someone read your text messages
Cart important points
Someone who is not physically in possession of your phone can forge your information for SMS spoofing. While you may not be able to control who gets your number, there are steps you can take to protect yourself.
Have you ever received a convincing text spoof message? What evidence did you have that it was a spoofed message? Email us. Cyberguy.com/Contact.
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report newsletter using the link below. Cyberguy.com/Newsletter.
Ask your cart a question or let us know your story you'd like us to feature.
Answers to CyberGuy frequently asked questions:
Ideas for how to use holiday gift cards
Copyright 2024 CyberGuy.com. All rights reserved.






















