Apple users are being urged to update their devices as soon as possible after CyberThruth reveals a major flaw that allows hackers to enter their gadgets.
What's called “Airborne” allows hackers to eavesdrop conversations when they deploy malware, snoop private data, and connect to the same WiFi network as devices that include public locations such as airports, coffee shops, and even work offices.
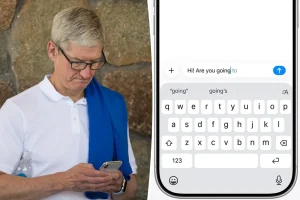
To keep hackers out, users are encouraged to update all their devices to the latest software, especially those connected to Airplay.
It is also a good idea to completely disable the airplay feature if you are not using it, as it acts as an access point to allow hackers to control the device.
Even worse? You are a device do not have It can be a different gateway for hackers, as if the bluetooth speaker is collecting dust.
“With AirPlay support on such a wide variety of devices, it can take many years to patch. I told Wired.
“And it's all because of a single software vulnerability that affects everything.”
Defects – Those 23, to be precise – Found in Apple's AirPlay Protocol and Software Development Kit (SDK). This allows users to beam photos, music and videos between devices.
While Apple has released security updates to fix defects in the device, millions of third-party gadgets, from smart TVs to set-top boxes to car systems, could be wearing ducks even when the manufacturer hasn't patched it.

This means that even if your iPhone is completely up to date, the connected speaker or TV can act as a backdoor, and hackers love the backdoor.
“If hackers have access to the same network as any of these devices, they can be used as a stepping stone to gain control and reach everything else,” warned Elbaz.
Patrick Wardle, a cybersecurity expert who is CEO of Apple-focused security company DoubleYou, also noted the outlet that these third-party time bombs are often ignored by users and the companies that made them.
“When third-party manufacturers integrate Apple technologies such as AirPlay through the SDK, Apple clearly loses direct control of the hardware and patching processes,” Wardle says.
As a result, he explained that if a third-party vendor drags his foot or skips an update completely, it could leave users exposed and reduce consumer confidence across the “Apple ecosystem.”