Security researchers have discovered new malware suspected of espionage. Hackers infect devices by posing as a government agency, usually a tax agency such as the Internal Revenue Service (IRS). Once on your PC, the malicious software can collect information (personal data, passwords, etc.), download additional malicious software, and upload data to the hacker's servers. All this is done while avoiding suspicion and storing the data using Google Spreadsheets.
For security alerts and expert tips, sign up for KURT's newsletter, The Cyberguy Report, here.
Illustration of a computer hacked by malware (Kurt “Cyberguy” Knutson)
It all started with a fake email
The hackers behind the malware, called “Voldemort,” have cleverly designed it to avoid getting caught, and it's causing problems in the cybersecurity world in the same way that the name Voldemort caused problems in J.K. Rowling's Harry Potter series.
The cyber attack begins when a victim receives an email that appears to be from a government tax agency. Proof PointsThe hackers behind this attack are impersonating tax authorities from a variety of countries, including the US (IRS), UK (HM Revenue & Customs), France (Direction Générale des Finances Publiques), Germany (Bundeszentralamt für Steuern), Italy (Agenzia delle Entrate) and, as of August 19, India (Income Tax Department) and Japan (National Tax Agency). Each email lure is customized and written in the language of the tax authority being spoofed.
Proofpoint analysts found that hackers customized phishing emails to match the target's country of residence based on publicly available information, rather than the organization's location or the language inferred from the email address. For example, some targets at European organizations received emails impersonating the IRS because public records linked them to the United States. In some cases, hackers mixed up the country of residence when targets shared the same name as prominent figures.
The emails imitate government emails – for example, people in the US received a fake “no_reply_irs” email.[.]gov@amecaindustrial[.]For more information, please visit www.salesforce.com.
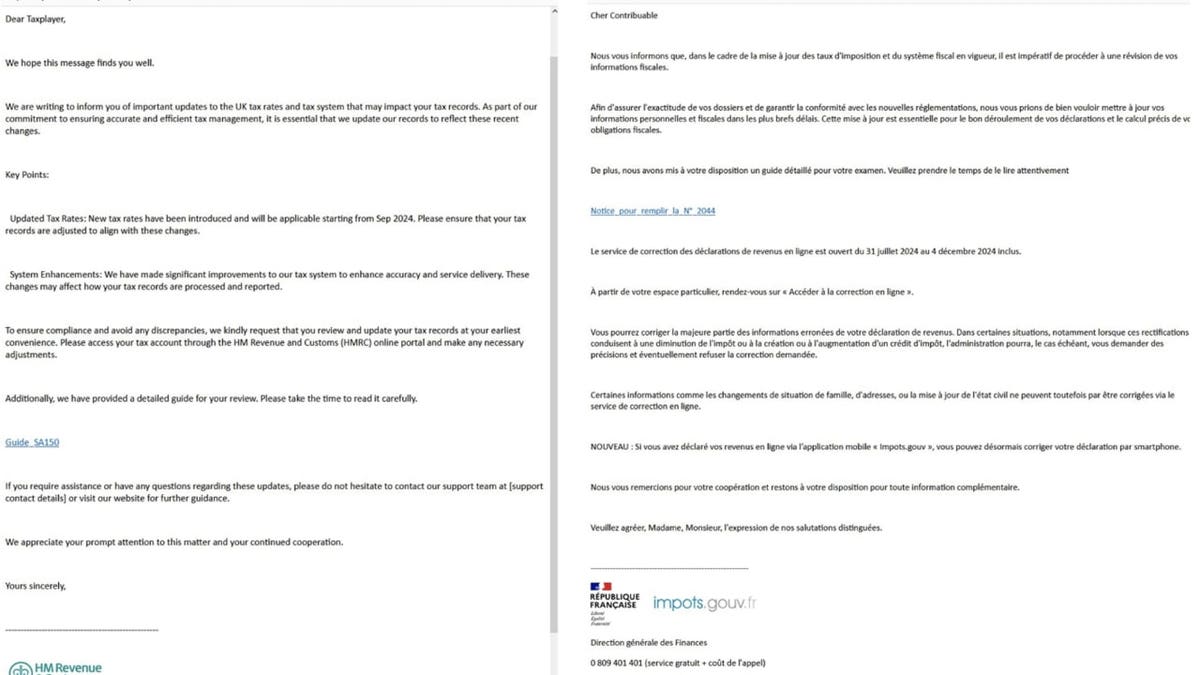
Emails attempting to impersonate government emails (Proofpoint) (Kurt “Cyberguy” Knutson)
The attack is deployed on your device
In the fake emails, hackers posing as government officials warn of changes to tax rates and regulations and ask users to click on a link to read a detailed guide. Clicking on the link takes them to a landing page that uses a Google AMP Cache URL to redirect them to a page with a “Click to view documentation” button.
Once you click the button, the hacker checks if you're using a Windows device, and if so, redirects you to another page. Interacting with that page initiates a download that appears to be a PDF file in your PC's Downloads folder, but is actually a LNK or ZIP file hosted on an external server.
When the file is opened, a Python script is executed from another server without the script actually being downloaded to the computer. The script collects system information to profile the user and opens a fake PDF to hide its malicious activity.
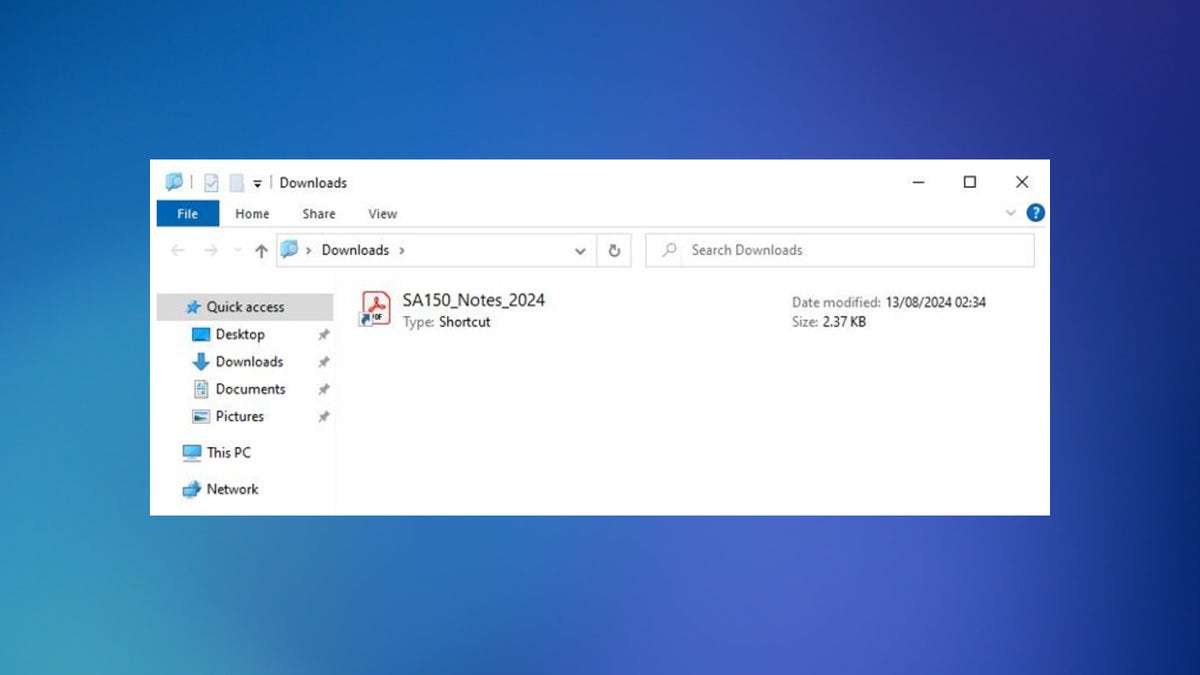
Downloads that look like PDF files in your PC's Downloads folder (Proofpoint) (Kurt “Cyberguy” Knutson)
Voldemort uses Google Spreadsheets to store his data
Once malware infects a Windows device, it can:
- pin: Check if you are still connected to the control server
- director: Get a list of files and folders on your system
- download: Sends a file from the system to the control server
- Upload: Put a file on the system from the control server
- Executive: Run a specific command or program on the system
- copy: Copy a file or folder on your system
- Move: Moving files and folders on your system
- sleep: Pauses activity for a certain period of time
- Exit: Stops execution on the system
The malware uses a Google Spreadsheet as a command center to get new instructions and store stolen data: each infected device sends data to a specific cell in the Google Spreadsheet, marked with a unique ID to keep everything organized.
Voldemort communicates with Google Spreadsheets through Google's API, using an embedded client ID, secret, and refresh token stored in encrypted configuration. Because Google Spreadsheets is widely used by enterprises, this method ensures that the malware can communicate without raising suspicion, making it difficult for security tools to block.
How to Recognize and Avoid Being a Victim of Vacation Rental Scams
4 ways to protect yourself from malware attacks
Hackers are releasing increasingly sophisticated malware, but that doesn't mean you're defenseless. Here are some tips to protect yourself from such attacks:
1) Read sensitive emails carefully. The best way to spot a fake malware-delivering email is to look carefully. Hackers may be tech-savvy, but their language skills are often not perfect. For example, in the screenshot above, you can see typos such as “Taxplayers” instead of “Taxpayers” – mistakes that government agencies would not normally make.
2) Check your email domain: Make sure the domain of the email matches the organization it represents. For example, emails from the IRS should be sent from an address ending in “@irs.gov.” Watch out for misspellings or variations in domains.
3) Invest in a data deletion service: Hackers will target you based on the information you have publicly available, which could be anything from information exposed in a data breach to information you provided to an e-commerce store. Check out my recommended data deletion services here.
4) Deploy powerful antivirus software: Having a strong antivirus software installed on your devices will protect you from receiving these fraudulent emails and accidentally opening attachments or clicking on links. The best way to protect yourself from clicking on malicious links that install malware that can access your personal information is to have antivirus protection installed on all your devices, which will also alert you to phishing emails and ransomware scams. We've handpicked the winners of the best antivirus protection of 2024 for Windows, Mac, Android and iOS devices.
Subscribe to KURT's YouTube channel for quick video tips on how to use all kinds of tech gadgets.
Important points about the cart
Although the researchers cannot say for sure, many of the techniques used by the malware are similar to those used by hackers suspected of espionage. Even if this assessment is incorrect, the scale and sophistication of the attack is concerning. Anyone with no technical knowledge could easily fall victim and lose personal information and money. The attack specifically targets Windows users, raising questions about Microsoft's security framework.
What steps do you think organizations should take to better protect individuals from malware attacks? Cyberguy.com/Contact Us.
If you want to receive more of my tech tips and security alerts, subscribe to the free CyberGuy Report newsletter at the link below. Cyberguy.com/Newsletter.
Have a question for Kurt or tell us the story you'd like to see featured?.
Follow Kurt on his social channels:
Answers to the CyberGuy's most frequently asked questions:
New Arrivals from Cart:
Copyright 2024 CyberGuy.com. All Rights Reserved.