New malware associated with a hacking group from Russia identified by Google

New Malware “LostKeys” Linked to Russian Hacking Group On Wednesday, Google announced the detection of a new malware named “LostKeys,” which is associated with a Russian hacking group called Cold River. This malware has the capability to steal files and transmit system information to the attackers. Wesley Shields from Google’s Threat Intelligence Group described this […]
Hackers using malware to steal data from USB flash drives

Cybercriminals are constantly finding new ways to steal data. As people become more aware of common threats like phishing links, fake websites, fraudulent emails, and spoofing scams, attackers are becoming more creative with their approach. One of the new ways they are using involves targeting USB flash drives. It may be surprising to focus on […]
ClickFix malware tricks you into infecting your own Windows PC

Clickfix is a social engineering trick that hackers are increasingly using to spread malware in early 2024. It tricks you into running malicious commands on your own computer, and attacks have become more common than ever. Hackers have them install password-stolen malware by pressing a series of keyboard shortcuts under the pretense of proving they're […]
Google Chrome confirms cyber ‘espionage’ attacks from ‘highly sophisticated malware’

Think about it before clicking on these links. After cybersecurity experts discovered an influx of malware infecting chrome users, Google has since I confirmed the attack We have announced security patches to help you update the latest browsers. Researchers at data protection company Kaspersky discovered “a wave of infections caused by previously unknown and sophisticated […]
FBI warns about document conversion sites spreading malware

Online document conversion sites have been a lifesaver, whether they needed to convert PDFs into editable documents, convert PPT to PDF, or open lesser known file formats. Most of these sites offer free and quick results, but many also pose serious privacy risks. Uploading a document essentially leaves you with no obligation to protect the […]
Malware steals bank cards and passwords from millions of devices

Infostealer malware is one of the biggest cybersecurity threats at the moment. There are many different types of this malware and comes with all kinds of names. Some are sold as software services. Hackers pay monthly fees to use to scam people, just like they pay to access Netflix. Infostealer's malware economy is clearly booming, […]
Dangerous malware targets you through fake loan app
Spyloan apps are everywhere But people keep falling for them. They promise simple loans with flexible repayments, but what they actually do is steal personal data such as contacts, confidential images, files and more. The moment you receive the loan, they will start blackmailing you using your own data against you. Some of these apps […]
New malware exploits fake updates to steal data
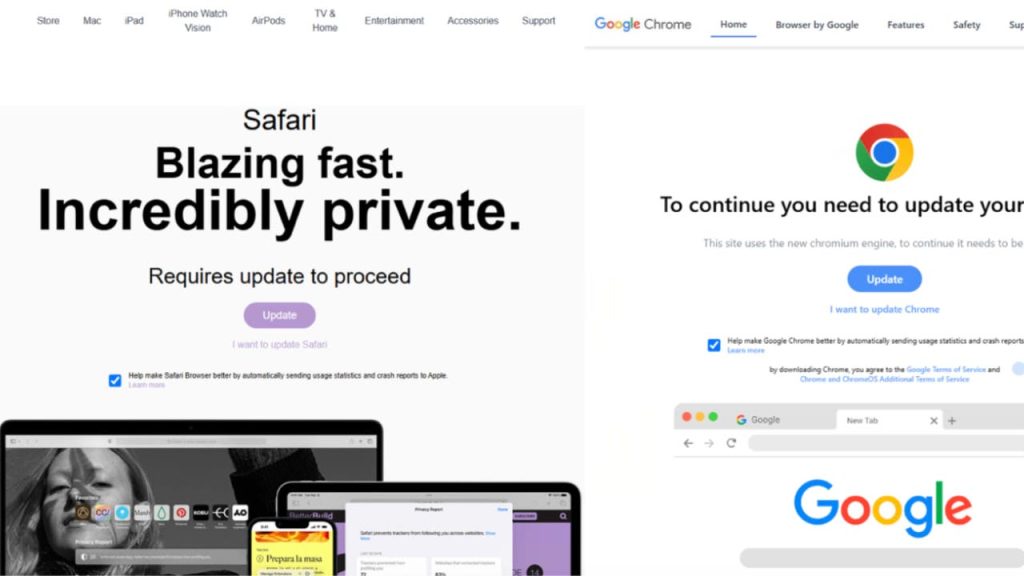
Windows has always been a favorite target for hackers, but it seems they understand how to actively target Macs. We've seen an amazing rise Malware affecting Mac computerssteal personal data and cryptocurrency. Threat actors are currently using AI to use elaborate social engineering tricks to target Apple users, but the company doesn't seem to do […]
Mac malware returns with advanced capabilities

It's early, but 2025 hasn't been a great year for Mac cybersecurity. Less than two months later, we saw numerous Mac malware threats targeting Apple laptops, which are generally considered very safe. These threats range from malicious software that can read screenshots and steal passwords from Infostealers. Now, Microsoft is identifying resurfaced malware that came […]
Nearly 4 billion passwords exposed by malware

Infostealer malware increased in 2024, hackers used it to steal credentials, cryptocurrency and other personal data from millions of users. If you remember, I reported countless times The Infostealer incident called Lumma Get Android, Windows, and even iOS and Mac users. A new cybersecurity report, along with hackers using Lumma and STEALC, Redline and other […]









