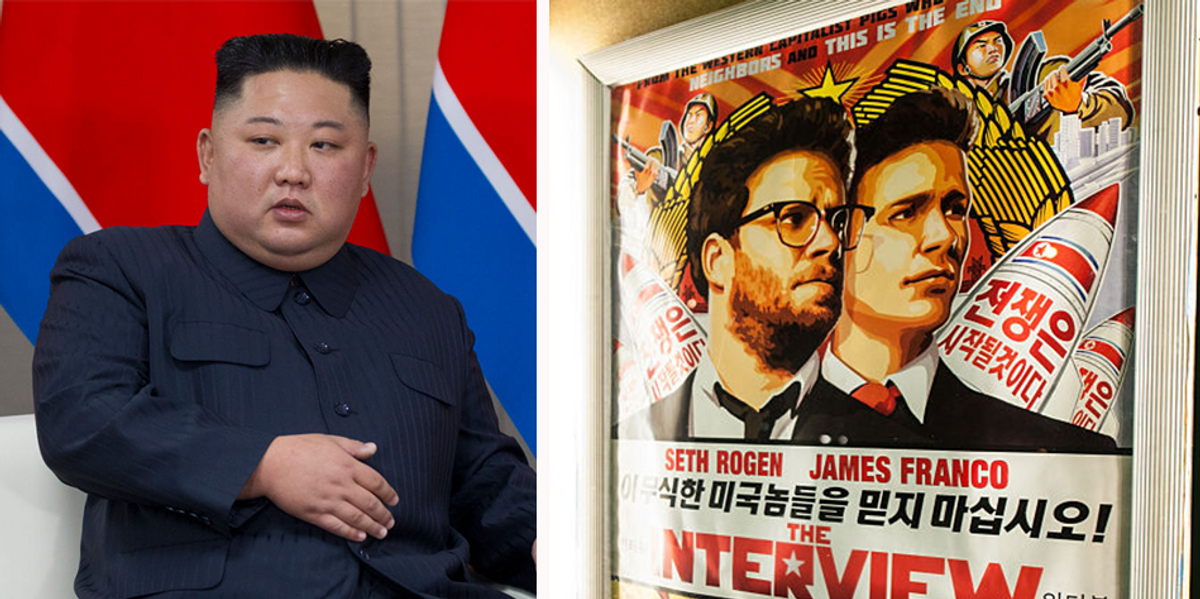
It's been 10 years since the Sony Pictures hacking scandal surrounding The Interview, a comedy starring Seth Rogen and James Franco.
In the film, Logan and Franco team up to interview North Korean leader Kim Jong Un in order to save his fading television career.
The film's storyline was allegedly too damning for the North Korean dictator, which led to North Korean hackers breaking into Sony Pictures' servers and leaking a trove of data, including tons of emails from Sony executives, including CEO Michael Lynton and co-chairman Amy Pascal.
“Usually it's the IT staff that you have to worry about.”
The initial report was released just four days after the hack on November 24, 2014. Recodeclaiming that the attack was carried out by North Korean organisations.
Guardian of the Peace
Initially, Sony received messages from a group calling itself “God'sApstls,” which were peppered with claims of unfair business practices by Sony.
“We have suffered great damages from Sony Pictures,” the message read in broken English. “We demand compensation, monetary damages. If the damages are not paid, the whole of Sony Pictures will come under attack. You know us well. We never wait long. Please act wisely.”
The Messengers of God were only mentioned again in a follow-up message by a group called the Guardians of Peace.
“We have already warned you, this is just the beginning and we will continue until our demands are met,” another group message said. deadline“I am deeply grateful to God's messengers for their great efforts for world peace,” he added.
This sparked suspicions that the hacking may not have come from a North Korean organization but from within Sony's own premises.
Cybersecurity expert Lukas Zajczykowski said: pointed out Back then, state-sponsored hackers didn't typically adopt catchy names like “Guardians of the Peace.”
“Attackers don't give themselves cool names,” he said.
Researcher Ken Heckenlively agreed, saying the hackers' messages “sound like they were coming from a group of disgruntled employees.”
In an interview with Blaze News, the author said he spoke to technology experts, cybersecurity companies and even former members of intelligence agencies, all of whom were skeptical of the government's official version.
“Not even the powers that be can stop this from getting out!” the author joked over a shaky internet connection before the feed stabilized and his book appeared.
The cover features a cartoon of Barack Obama and Kim Jong Un battling like Godzilla and Rodan in front of a Hollywood backdrop, but the subject matter inside is much more serious than the cover would suggest.
Inside the Sony hack: A look behind America's most notorious near-war cover-up
Heckenlively explained that several cybersecurity agencies stepped up in 2014 to try to save the day.
He called cybersecurity agencies “like bounty hunters who want to play hero to big tech companies.”
Cybersecurity firm Norse accepted the request and began its investigation in late December 2014.
“Sony underwent significant staff cuts in 2007. [May] “We had a lot of IT staff cases in 2014,” Heckenlively told Blaze News, “and a lot of it was about IT staff. Usually, IT staff are the ones we have to worry about because they have access to the network.”
“immediately [Norse] “The hack was carried out by an insider using another hacker group called Lizard Squad, who have previously hacked Sony PlayStation,” Heckenlively said, highlighting another interesting hacking group name.
that hackThe attack, which occurred just a few months ago in August 2014, took down the PlayStation Network, Xbox Live and Facebook.
“But that's not the story the US government wanted,” the author continues. “It was North Korea's work! It was Kim Jong Un's work! … But North Korea didn't have the capacity to do it. The hack was done by an insider, possibly physically present on Sony's premises.”
Kurt Sternberger, then a senior vice president at North, presented the findings to the FBI, which also suggested the break-in was an inside job.
“Sony wasn't just hacked. The company was essentially nuked from the inside,” Sternberger said. CBS News“We believe this was not an attack masterminded by North Korea and that insiders played a key role in carrying out one of the most devastating attacks in history.”
Sternberger argued that the security lapses likely stemmed from six disgruntled former employees who were fired in early 2014.
However, this wasn't a case of Norse rebelling against the government, and other cybersecurity experts agreed with the company.
Michael Hiltzik, columnist for the Los Angeles Times Characteristics of the evidence He cited “circumstantial evidence” that North Korea was involved, and said other experts were “skeptical” about any link between the attack and the North Korean regime.
Kim Zetter of Wired Explained He called the evidence against the North Korean government “weak” and doubted the actual hackers had any ties to North Korea.
Hector Monsegur, who previously hacked Sony with a group called Anonymous, said the recent attacks on the company had happened too quickly.
“For something like this to happen, it had to happen over a long period of time. You can't steal a terabyte or 100 terabytes of data in a few weeks,” he said. CBS News.
Monsegur questioned whether North Korea's limited internet infrastructure would allow it to manage such a transfer, and suggested the attack could have been carried out by hackers backed by China, Russia or North Korea, but leaned more toward it being an inside job by Sony employees.
Why Sony?
Critics have long pointed to a possible cover-up by U.S. intelligence agencies, but the lack of direct evidence of North Korean involvement has only strengthened those allegations.
According to most reports, it took seven to nine days after the hack for North Korea to be singled out as the culprit. The Hollywood ReporterIn 2000, it took the FBI just 25 days to identify Guardians of Peace as working for the North Korean government.
The reasons for the cover-up are numerous and never-ending.
One of the reasons is that Corporate Terrorism Risk ProgramThis federal program provides compensation to businesses that suffer losses as a result of terrorist acts.
The “temporary federal program” was established after 9/11 and was reauthorized in January 2015, just two months after the Sony hack. The program has been renewed twice and is valid until December 31, 2027.
According to the program 2024 ReportThe program paid $56.7 billion in premiums to insurers between 2003 and 2023.
Heckenlively's clearest explanation was for another reason for the cover-up: to foment conflict between North Korea and the United States that would benefit the military and intelligence contractor RAND Corporation.
It turns out that Sony's connection to the organization was through former studio head Linton, who was on RAND's board at the time. Email In the data dump.
“Linton's father was in British intelligence and served on the board of directors of the RAND Corporation,” Heckenlively noted. [Amy] “Pascal's father.”
Contacts between Mr. Linton and Ms. Rand revealed that the organization wanted to invite stars such as George Clooney to its events and that Mr. Linton had offered a contract to Valerie Jarrett, an adviser to President Barack Obama.
Simply put, Sony executives had deep ties to people with direct ties to the federal government.
“I thought he was a really good guy and he just wanted to know the truth.”
The Seth Rogen Factor
The conspiracy allegedly began when Logan and his writing partner Evan Goldberg submitted “The Interview” as a script.
“The film was originally an unnamed, ambiguous [leader]”It's a lot like the Sacha Baron Cohen film The Great Dictator,” Heckenlively explains, “but partway through development, a Sony executive suggested making Kim Jong Un the film's antagonist.”
When asked if Logan was aware of Sony's relationship with Lando as the reason for the change, Heckenlively pointed to comments the actor made to The Hollywood Reporter in 2019.
Rogen said at the time that he had never been targeted by North Korean organizations. [his] head.”
“This doesn't seem like the North Korean way. It seems more like the work of young, amateur hackers than a foreign government launching a coordinated attack on another country,” he said.
“It would be nice to know the truth,” Rogen added, after suggesting North Korea may have been used as a cover.
“I don't think it would make much difference to me personally whether it was North Korea or not, but I think other people would probably feel vindicated,” he concluded.
Throughout all of her research, Heckenlively made sure to highlight the fact that she was pleasantly surprised by the way Rogen handled the ordeal.
“I thought he was a really good guy and he just wanted to know the truth,” Heckenlively said.
The author smiled at the idea that there were people in Hollywood who wanted to know the truth.
Ultimately, Heckenlively came to a simple conclusion: intelligence agencies work with film studios to produce provocative, purposeful entertainment.
Whether it's foreign policy based or to push for specific legislation, government agencies may be more entrenched in Hollywood than the public realizes.