North Korean engineers are using artificial intelligence and other technologies to defraud foreign governments and companies, obtain jobs overseas and earn U.S. dollars to fund Kim Jong Un's regime, Asia Nikkei Review reported Thursday.
According to the Nikkei Shimbun, American intermediaries are helping the North Korean regime obtain foreign currency to fund its weapons program. The paper mentioned that case Matthew Isaac Nute, 38, of Nashville, Tennessee, ran a “laptop farm” to generate income for North Korea's weapons program.
Using this equipment and stolen personal information, Noot tricked American and British companies into hiring North Koreans posing as American IT workers in remote locations and gaining profits on remote IT jobs. and laundered the proceeds into accounts associated with parties in both North Korea and China. The “laptop farm” operation netted more than $250,000 per fake worker from July 2022 to August 2023, according to the Middle District of Tennessee Attorney's Office.
American authorities reportedly discontinued the Noot operation in August. He has been charged with aggravated identity theft and conspiracy to commit illegal employment of aliens, and if convicted, he could be sentenced to up to 20 years in prison.
Tennessee 'laptop farm' appears to have infiltrated US tech companies using forged or stolen personal information to fund North Korean regime and potentially conduct cyberattacks and intrusions It is the latest in a growing list of similar incidents involving North Korean officials.
Published by Google's security subsidiary Mandiant. report In September, it detailed the plans of a North Korean hacker group known as UNC5267 dedicated to infiltrating US tech companies. Although the group does not operate as a “traditional centralized threat group,” it has been active since at least 2018, according to the report. Its members are dispatched from North Korea and live in China and Russia; some of them live in China and Russia. To countries in Africa and Southeast Asia.
The group uses stolen personal information to apply for various remote jobs or to be brought into businesses through contractors. Some work multiple jobs at once, generating millions of dollars in income for the North Korean regime.
“We have eliminated more than 50 candidates who were North Korean spies,” said Lili Infante, founder and CEO of CAT Labs in Miami. It got to the point where we had to introduce it.” -based cybersecurity startup, said of wall street journal In June.
Similarly, cybersecurity firm KnowBe4 revealed In July, the company announced it had discovered a North Korean spy posing as a remote software engineer from an internal team. KnowBe4 Description Website They received the North Korean spy's resume, conducted an interview, and conducted various background checks, and announced that the spy appears to have passed them.
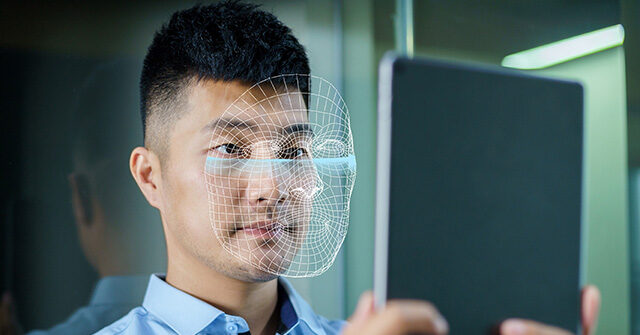
Once the workstation devices were sent, North Korean spies immediately began loading malware onto the company's network. The spy was able to deceive the company by using a stolen US-based identity and using artificial intelligence to digitally alter stock photos.
Since May, the US has provided $5 million. bounty Any information that could lead to disruption of North Korea's financial networks, as well as remote jobs with US companies using over 60 stolen US identities, resulting in at least $6.8 million to North Korea. Information about the North Korean IT workers who generated the profits will be targeted.
Christian K. Caruso is a Venezuelan writer who chronicles life under socialism. You can follow him on Twitter here.