Many of us have families to take care of. We save money not only for our future, but for our children and grandchildren, and perhaps even more. We want to ensure a good education and help them buy a home or simply secure something when they need it.
So did Tony. He saved quite a bit of money for his son's future and saved over $4 million in Bitcoin. And with just one click He lost it all to Visinga type of scam that uses phones to trick people into giving up sensitive information.
The con man posed as a Google Support Agent, after an elaborate scheme, first attracted his attention, then gained his trust, and ultimately left him nothing.
“Please, man. Is there anything I can do to give something back?” It was Tony's final, hopeless plea to the con man, hoping to appeal to their humanity.
Man typing on a computer keyboard (Kurt “Cyberguy” Knutsson)
What is Vising?
Vising“Voice Phishing,” is a type of cybercrime that uses telephones to call to reveal personal and financial information to deceive individuals. Unlike Traditional fishingrelying on email and text messages, leveraging the power of human voice and social engineering to manipulate victims. Scammers often impersonate legal organizations such as banks, tech companies, and government agencies to gain trust and create a sense of urgency. They may request a password, credit card number or other confidential details.
Vishing relies heavily on social engineering tactics, which can be difficult to detect, making it a particularly dangerous cybercrime.
Hacker illustration at work (Kurt “Cyberguy” Knutsson)
Best antivirus for Mac, PC, iPhone and Androids – CyberGaipic
Scars are well edited plays
Let's break down these vishing schemes and understand why they are so effective. Viewing them as a step-by-step play consisting of various actions makes it easier to recognize individual tactics.
Act 1: Setup and Targeting
Scammers start by identifying potential victims through social media, public transaction records, leaked databases, and more. Selecting a target will collect personal information (email, phone numbers, financial holdings) to increase reliability. And you can easily become a target. That's why Data Broker – A company that buys and sells your personal information – Goldmine is for fraudsters. Your entire profile could be there, Includes everything you need to carry out a successful scam: Your name, address, contact details, family, property ownership, etc.
How to protect yourself at this stage:
- Limit yours Share onlineespecially financial details
- Sign up Data deletion service This will erase your personal information from your company's database.
Act 2: First Contact
Scammers always start contacting you first. For example, use your Google account to walk through Vishing Scam.
- Triggering the actual security alert: Scammers may try to recover your Google account to encourage actual security alerts, such as verification codes sent to your phone. Their goal is not to reset your password, but to make them believe there are real security issues.
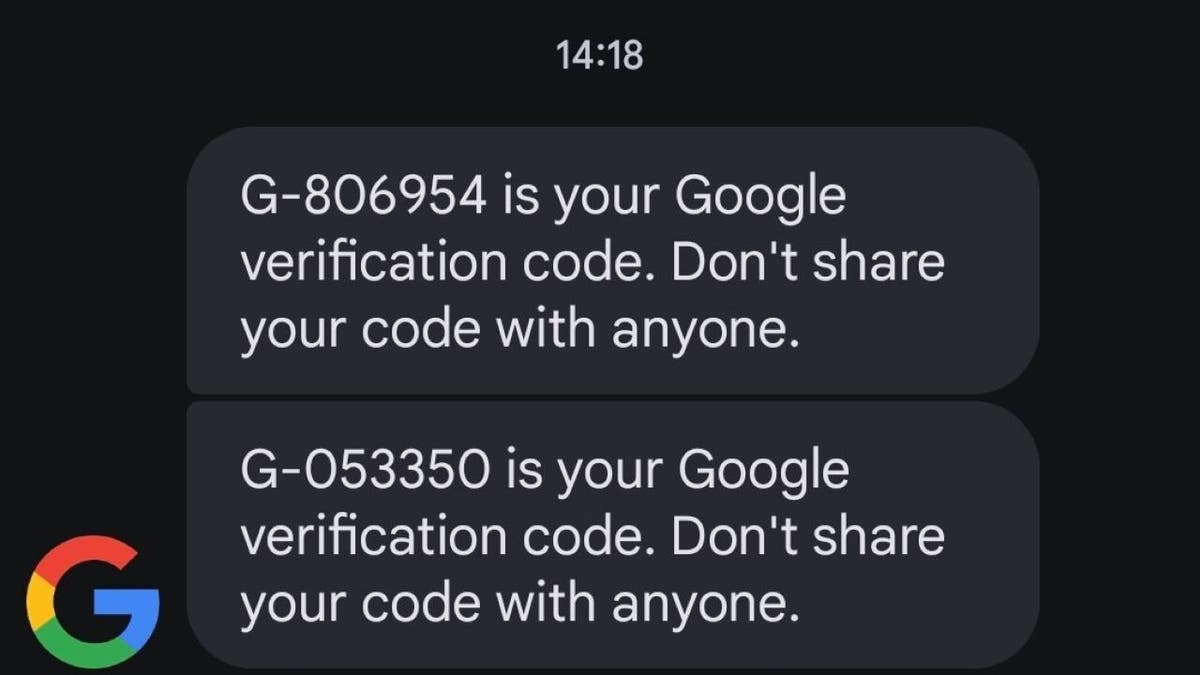
Google Verification Code Text (Kurt “Cyberguy” Knutsson)
- Sending fake security messages: Create fake Google Forms using your email address, designed to mimic official security alerts. This message often claims that there has been a security breach and that the appointed support agent will contact you immediately.
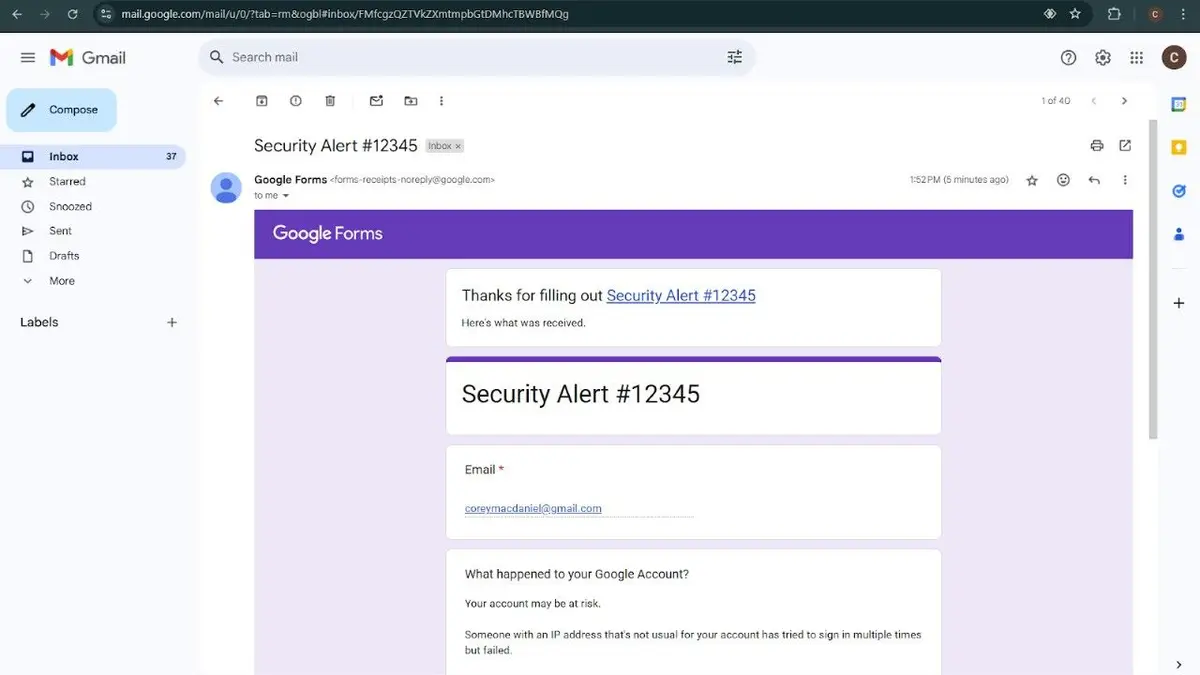
Fake Google Forms (Kurt “Cyberguy” Knutsson)
- Make a call: Immediately after receiving the email, the scammer will call using a spoofed Google number and guide you through fake security steps.
How to protect yourself at this stage:
- Pause and check – Actual companies should not call or email you for sensitive security actions
- Contact the company directly – Use official contact details (don't trust caller numbers or emails)
- Being skeptical of emergency security warnings – Scammers create fake emergency situations to make you act without thinking
How to delete private data from the Internet
Act 3: Building Trust
Scammers no longer ask for passwords altogether. That trick doesn't work anymore. Instead, it's what they do.
- Introducing yourself as a support agent: They claim to be gentle and friendly and are here to help investigate the issue. They refer to the details of fake Google Forms in a legitimate way.
- Walk through the actual password recovery process: Over the phone, the scammer will instruct you to change your password as a security measure. They don't send suspicious links, but instead guide them through the actual recovery process. At this point they still have no access to your account. But it is about to change.
What is Artificial Intelligence (AI)?

Illustration of username and password credentials (Kurt “Cyberguy” Knutsson)
Act 4: Fraud
After successfully resetting your password, the scammer will ask for the final step: Log in. This is where the actual scam occurs.
- Send phishing link: Because you trust them, they send messages using a spoofed Google number with a link to login. However, the link leads to a phishing site designed to look like a Google login page.
- Log in to the actual site: As soon as you enter your credentials on a fake page, the scammer will enter them into the actual Google site. After a few seconds you will receive a real Google security prompt asking, “Is this you?”
- Click “Yes, that's me” to complete the scam: While you were on their fake platform, they were logged in to your actual account simultaneously using your credentials. Google Security Prompt? It wasn't for your device. It was for them. As a result, scammers can now access your account.
How to protect yourself at this stage:
- Do not log in to your account Use the submitted link
- everytime Please check the URL Find the correct spelling “https://” before entering your credentials
- Use a Password Manager It is automated only to legitimate sites. A high-quality password manager guarantees security with zero-knowledge encryption, military-grade protection, and support for multiple platforms including Windows, MacOS, Linux, Android, iOS, and major browsers. Look for features like unlimited password storage, secure sharing, password health reporting, data breach monitoring, autofill, emergency access and more. Check out my experts' best password managers for 2025
Hidden Costs of Free Apps: Your Personal Information
Act 5: Robber
At this stage, the scammer will finish the phone and you are relieved. You never realize what happened until it's too late. And it's not just about Google accounts. You can use the same method to access your Apple account, banking services, and cryptocurrency wallets. For some, losing access to Google alone is devastating. After all, Google Drive, Google Photos and other cloud services have a huge amount of personal and financial data. But by the time we realise what happened, it's already too late.
How to protect yourself at this stage:
- Protect your account now -Reset your password, enable two-factor authentication in the Authenticator app, log out of all active sessions, and remove unauthorized access.
- Report and monitor fraud – Warn your bank, credit card provider or crypto exchange and freeze your transactions if necessary. Report a scam to the FTC (Reportfraud.ftc.gov), IC3 (ic3.govand affected platforms. Monitor your account for suspicious activity and consider credit freezes to prevent identity theft.
It's very important to secure an account and report a scam after a fraud has already happened, but the best defense is to prevent these attacks in the first place. By taking these measures, you can avoid falling victim to fraudulent fraud in the first place.
How to protect yourself from fraud
1. Invest in personal data removal services: All of these scams have one thing in common. They need some of your personal information to work. Without your name, phone number and email, these scams won't happen. Scammers may even try to gain your trust by making them more trustworthy in your personal information, such as your Social Security number. We strongly recommend that you remove personal information from people's search sites online. Give someone an email or phone number and they may be able to find their home address in reverse search. Although there is no service that promises to delete all data from the internet, deleting a deletion service is great if you want to constantly monitor and automate the process of continuously deleting information from hundreds of sites over a long period of time. Check out our top picks for data deletion services.
2. Set recovery contacts: Make sure you have a backup contact for your account (Google, Apple, Bank) and have a way to regain access if you are locked out.
3. Monitor your financial account: Check your financial account regularly for suspicious activity or fraudulent transactions.
Click here to get your Fox business on the go
4. Enabling 2-factor authentication (2FA): Enable 2FA All accounts, especially Google, Apple, Financial Services. This adds an extra layer of security and makes it difficult for scammers to access your account even if they obtain login credentials.
5. Secure Devices: Make sure your device is protected Screen lock or biometric authentication And I'll keep it Latest Software To prevent malware attacks.
6. Report fraud quickly: If you are being scam, please report the scam immediately to the FTC Reportfraud.ftc.gov Notify affected platforms.
7. Use powerful antivirus software: Periodically install and update powerful antivirus software to protect your device from malware, viruses and other cyber threats. Antivirus software helps prevent infection by providing real-time protection, scanning for malicious files, and blocking access to harmful websites and downloads. The best way to protect yourself from malicious links to install malware is to install powerful antivirus software on all your devices, as it may access your personal information. This protection can also warn you that it will phish email and ransomware scams and keep your personal information and digital assets safe. Get the best 2025 Antivirus Protection Winners picks for Windows, Mac, Android and iOS devices.
Important takeouts for your cart
Tony's story is a horrifying reminder that even the hardest-working savers can fall victim to sophisticated fraud. These vishing schemes are carefully tuned like theatrical plays, exploiting trust and leveraging real security alerts to access your account. Protecting yourself requires constant awareness, skepticism about unsolicited communication, and proactive measures to protect your personal information. Tactics may evolve, but the underlying principles remain the same. Scammers rely on deceptions to exploit our vulnerabilities. Understanding their methods and taking precautions can make it difficult for them to succeed.
Click here to get the Fox News app
What more do you think businesses and governments should do to combat this growing threat? Write us and let us know cyberguy.com/contact.
For more information about my tech tips and security alerts, sign up for our free Cyberguy Report Newsletter cyberguy.com/newsletter.
Please ask your cart or tell us what stories you would like us to cover.
Follow your cart on his social channels:
Answers to the most asked Cyber Guy questions:
New from Cart:
Copyright 2025 cyberguy.com. Unauthorized reproduction is prohibited.