X, previously known as Twitter, has recently created a headline, with Elon Musk claiming that hackers are trying to disrupt the platform. However, the latest news involving social media sites is particularly surprising, putting users at serious risk.
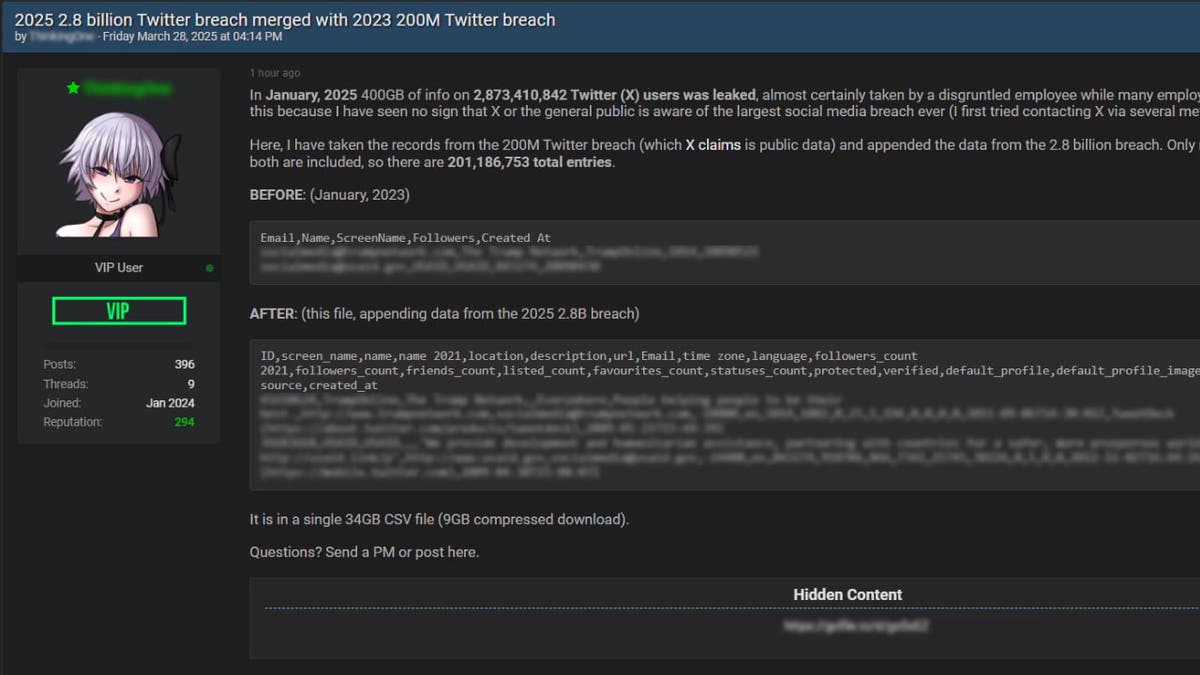
Earlier this month, reports of major data breaches including X were revealed after a self-proclaimed data enthusiast known as “ThinkingOne” allegedly released a database containing more than 200 million user records to a popular hacker forum. The leaked data includes your name, email address, and almost everything else associated with the user's X profile.
iPhone X App (Kurt “Cyberguy” Knutsson)
What you need to know
The X Data Leak is believed to be attributed to a combination of violations, including the large-scale ones that allegedly occurred in January 2025 and another large-scale ones in 2023. Profile image.
Thinkingone claimed that the data was cross-referenced from a major violation that included 2.8 billion unique Twitter IDs and screen names. The violation may have been linked to insider's work during the layoffs on X, but the company has not confirmed this claim. Includes cybersecurity researchers from Safety detectivewe partially verified the reliability of the data by matching the sample with the public x profile and verifying several email addresses. However, the ownership was not fully confirmed.
The violation appears to date back to a vulnerability identified through Twitter's bug bounty program in January 2022. This flaw allowed the attacker to access user data using only an email address or phone number. The vulnerability has been patched, but the compromised data appears to have resurfaced in a later leak.
Partial check of data (safety detective) (Kurt “Cyberguy” Knutsson)
Malware reveals 3.9 billion passwords with huge cybersecurity threats
Data breaches put X users at risk
Although the 2025 incident alone does not include passwords or financial information, when combined with email addresses from the 2023 leak, the risk of phishing and social engineering attacks increases dramatically. X has not officially admitted this particular violation at the time of writing, but previously downplayed the 2023 incident, but mainly included public data.
The total record of 2.8 billion is well over the estimated 33.5-600 million active users for X, suggesting that the dataset could contain inactive accounts, bots, or historical data. The full scope and impact of the violation remains unknown, but the incident highlights the ongoing security challenges of the platform, particularly after XAI acquired it in late March 2025.

Smartphone X logo (Kurt “Cyberguy” Knutsson)
How to delete private data from the Internet
Seven ways to stay safe from X data breaches
If you have an account on X, or if you think your data may be part of a violation, here are seven important steps you can take to protect yourself.
1) Use powerful antivirus software
The violation included an email address linked to your X account, and Prime Fuel for phishing attacks. Hackers can send an email that appears to be X, Musk, or Support and ask for “confirm your account” or “reset your password.” These often contain links or attachments that allow you to install malware or steal personal data.
The best way to protect yourself from malicious links to install malware is to install powerful antivirus software on all your devices, as it may access your personal information. This protection can also warn you that it will phish email and ransomware fraud and keep your personal information and digital assets safe. Get the best 2025 Antivirus Protection Winners picks for Windows, Mac, Android and iOS devices.
2) Delete personal data from the Internet
This X-leak has published details about your full name, email address and other public profiles, so hackers can easily cross-referencing with other data broker sites to build a complete profile for you. This can lead to impersonation and spear washing.
To reduce exposure, use a trusted data deletion service that scans the data broker's website and requests the removal of personal information. Although there is no service that promises to delete all data from the internet, it is great to remove deletion services when monitoring and automate the process of continuously deleting information from hundreds of sites over a long period of time. Check out our top picks for data deletion services.
3) Change your X account password
This particular violation may not include a password, but there is still a significant risk, especially when using the same password on multiple platforms. Once an attacker receives your email, they often use it with a common or previously leaked password to split it into accounts.
To change your X account password, go to Settings and privacy Select from the Profile menu Your account Tap Change your password. Enter your current password, set a new strong password, and confirm the changes. You can do this via a mobile app or by logging in from the web. Consider using a password manager to generate and store complex passwords. Get my details Find the best expert reviewed password managers of 2025 here.
4) Make your X profile more private to reduce future risks
Adjust your X account privacy settings to limit the visibility of your personal information, such as making your profile private. Make sure only the information you need is published. Information that you think is harmless, such as your location, title, or birthday, can be used by cybercriminals to impersonate you or guess your login credentials. If your X profile contains unwanted personal information, now is the time to delete it.
Minimizing your profile not only protects your privacy, but also makes it difficult for scammers to create compelling phishing messages and social engineering attacks. Think carefully before publishing your personal update or details, especially if it can be used to guess your password or verify your identity.
I'm going Settings > Privacy and Safety Lockdown account visibility.
5) Enable 2-factor authentication (2FA) for X and email accounts
If a hacker receives an email from an X-breach, he may try to reset his password. 2FA It helps to stop this by having to log in with the second code.
- Use authentication apps such as Google Authenticator or Authy rather than SMS.
- It also protects email accounts as they can be used to reset X credentials
6) Use a VPN with Public Wi-Fi
Protect your data when you access X or other platforms on a public network by encrypting connections using a VPN. This helps prevent you from being intercepted by malicious actors. A trusted VPN is essential to protect your online privacy and ensuring a secure, fast connection. For the best VPN software, see our expert reviews on the best VPNs for personal browsing the web on Windows, Mac, Android and iOS devices.
7) Sign up to catch identity theft protection if your X-linked information is being abused
Scammers may open an account with their names or use email in attempts to conceive, as more than 200 million people have publicly published names and email addresses. Excellent identity protection can alert you if your information is sold on the dark web. It also helps to freeze bank and credit card accounts to prevent further fraudulent use by criminals. See my tips and best choices on how to protect yourself from identity theft.
New Phishing Scams Carry Security Codes to Steal Your Information
Important points of cart
X violations are another reminder that patching vulnerabilities is just one of the much bigger puzzles. Persistence of leaked data – years after the original defects were disclosed and fixed, highlighting the long tail of exposure with large-scale violations. Even if your credentials aren't involved, combinations of identifiers such as email addresses, names, and social connections can be weaponized through correlation attacks, data enrichment, and AI-assisted social engineering.
Do you think companies are doing enough to protect your data from hackers and other cyber threats? Write us and let us know cyberguy.com/contact.
For more information about my tech tips and security alerts, sign up for our free Cyberguy Report Newsletter cyberguy.com/newsletter.
Ask us a question in our cart or let us know what you want us to cover.
Follow your cart on his social channels:
Answers to the most accused Cyber Guy questions:
New from Cart:
Copyright 2025 cyberguy.com. Unauthorized reproduction is prohibited.


















