Please try to imagine. You are sitting in your living room and feeling completely safe under the watchful eye of your home security camera.
But what if we told you that this camera designed to protect you could itself be violating your privacy? northeastern university We might all be looking over our shoulders.
Researchers have discovered that a stealth technology called EM Eye allows camera eavesdropping, turning trusted parents into unwitting accomplices.
home security camera (Kurt “Cyber Guy” Knutson)
How this technology eavesdrops on the inner workings of cameras
EM Eye is like a tech-savvy thief, but instead of picking locks, it picks up electromagnetic whispers from the inner workings of cameras. Like a radio tuned to a secret frequency, EM Eye listens to the radiation emitted by the camera’s wires. Unbeknownst to many, it can also act as an unwanted radio transmitter. The bits and bites that make up your video feed leak into the air, but EM Eye catches them all, making the walls around your camera as important as the air it records.
Don’t let porch pirates steal your stuff with these home security systems

home doorbell camera (Kurt “Cyber Guy” Knutson)
More information: Privacy win: Amazon limits police access to your Ring camera
EM Eye also targets drive recorders and smartphones
This technique is much more than just looking through the viewing window of a home security camera. The range extends to your car’s drive recorder and the smartphone you carry.
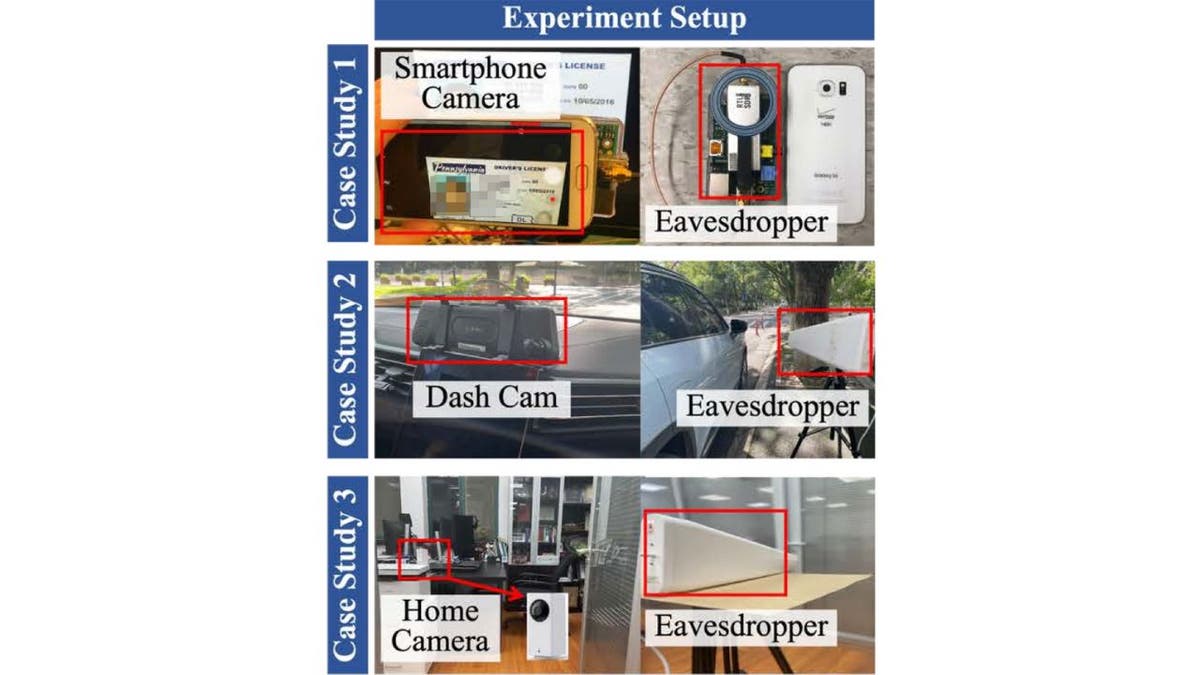
Experimental setup (Northeastern University)
The researchers cast a net over 12 different cameras and found that the distances at which video could be hijacked varied. Some are just a few steps away, others as little as 16 feet away. The 12 devices include 4 smartphones, 6 smart home cameras, and 2 dash cams. All of these devices were in their original packaging prior to testing. The make, model, and year of each device tested are listed below.
- Google Pixel 1 (2013)
- Google Pixel 3 (2018)
- Samsung S6 (2015)
- ZTE Z557 (2019)
- Wise Campan 2 (2019)
- Xiaomi Dafang (2019)
- Baidu Xiaodu X9 (2023)
- Taegong Mao (2023)
- Goob V9 (2022)
- Qiaodu (2021)
- 360 M320 Drive Recorder (2020)
- Blackview Dash Cam (2022)
We reached out to the companies that make these products for a response, but did not receive a response by deadline.
Read more: Are doorbell cameras susceptible to jamming and interference?
EM Eye’s Machine Learning Twist
Now, before you think everything is blurry and confusing, wait a minute. Yes, the video will be transmitted a little distorted, like a TV struggling to get a signal, but then there’s a twist: machine learning. Researchers wield this tool like master artists, refining and enhancing images until they look nearly identical to the original.
Read more: Tips from incredibly expensive conversations with cybercriminals
A wake-up call against reliance on supposedly safe technologies
Announced at a prestigious ceremony IEEE Symposium on Security and Privacy, EM Eye does more than just raise your eyebrows. It raises alarms about privacy and security. This is a wake-up call that the very devices we rely on for security may be working against us. With a little engineering know-how and inexpensive equipment, someone can become a video voyeur without leaving a digital footprint.
The brains behind EM Eye are more than just prophets. They are also problem solvers. They are asking camera manufacturers to do three things:
1) Wrap the camera wire in a special shield, like armor, for signals. This prevents electromagnetic waves from leaking out.
2) Please shorten the wire. The shorter it is, the less leakage it can capture.
3) Develop a better way to transmit camera signals. Think of it like speaking in a secret code that is difficult to decipher.
CLICK HERE TO GET FOX BUSINESS ON THE GO
How EM Eye turns your camera into a silent spy
The working principle is electromagnetic induction. This concept may go back to high school physics. The wires inside the camera are more than just cables. This is a book that anyone with the right antennae can read.
The researchers’ toolkit includes software-defined radios and directional antennas to locate cameras and send their electromagnetic signals back into video, like detectives following a trail.
unlike others spy tactics If you need to hack into a network or intercept cloud storage, EM Eye is your ghost operation. There is no need to touch the camera’s network or storage, and it is equally effective on offline devices such as car cameras. EM Eye’s potential extends to any device with wires that carry video data, including laptop screens, tablets, and even desktop monitors.

home security camera (Kurt “Cyber Guy” Knutson)
More information: How to detect a hacker spying on your doorbell camera
What can you do to protect your privacy?
EM Eye technology raises significant privacy concerns, but here are steps you can take to reduce the risks.
For home security cameras
Select a shielded camera. Look for cameras that are explicitly advertised as having shielded cables or built-in shielding against electromagnetic interference. This can greatly reduce video data leakage.
Minimize cable length: As the researchers noted, shorter cables emit less radiation. Choose a camera with a short built-in cable, or minimize the length of extension cables used.
Position the camera carefully. Avoid installing the camera near windows or exterior walls, as the signal can be easily intercepted. Consider placing them indoors to face the outdoors.
Avoid keeping cameras running inside your home. While you may think running cameras in your home will increase your security and peace of mind, it can also expose you to new threats. If cameras are not properly shielded and protected, video data can be leaked via electromagnetic signals and can be picked up by malicious attackers using EM Eye technology. This allows them to spy on your private activities, steal your personal information, and even blackmail you.
Disable unnecessary features. Turn off features like night vision and voice recording when not in use. These features may generate additional electromagnetic signals that can be exploited.
Keep your firmware up to date. Manufacturers may release firmware updates that address security vulnerabilities, including exploits similar to EM Eye. Regularly update your camera’s firmware by opening the app that controls your camera’s settings.
For other devices
Please be aware of your surroundings. When using devices with video output, such as smartphones, laptops, and tablets, be aware of the environment and potential eavesdroppers. Avoid use in sensitive areas or situations where privacy is important.
Use a webcam cover. By using webcam cover, you can prevent anyone from seeing you through your camera without your permission. Webcam covers can be used on any device with a camera, including laptops, tablets, smartphones, smart TVs, and game consoles. It’s best to cover your webcam, but you can also physically cover the camera with tape when not in use to prevent unauthorized access.
Use the privacy screen. privacy screen Laptops and tablets limit the viewing angle of the screen, making it difficult for someone to observe your activity from the side.
Invest in a Faraday bag: If you need high security, Faraday bag or Faraday shieldan enclosure used to block electromagnetic signals and optionally shield certain devices.
Although these steps can help reduce risk, they may not completely prevent eavesdropping by advanced technology. It is important to stay informed about new developments and potential remedies for EM Eye technology. By taking proactive measures and staying informed, you can protect your privacy in the face of evolving security challenges like EM Eye.
Cart important points
There’s more than just research here. That’s a statement. The argument is that in a world wired and monitored by cameras, privacy is a veil that can be lifted by those who know how to pull the strings. When you peer into your screen, it might be time to think about who you’re peering into.
CLICK HERE TO GET THE FOX NEWS APP
To protect us from this type of spying, is it time to ask home security and dash cam manufacturers to build cameras with encryption? Let us know by emailing us. Cyberguy.com/Contact.
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report newsletter using the link below. Cyberguy.com/Newsletter.
Ask your cart a question or let us know your story you’d like us to feature.
Answers to CyberGuy frequently asked questions:
Copyright 2024 CyberGuy.com. All rights reserved.